Despite the claims on their website, tvlicensing.co.uk are sending personally identifiable information and bank details in plain, unencrypted text.
The TV Licence website is not secure
When looking at the official UK TV licensing website today, I noticed when I started the payment procedure that Google Chrome clearly marked the website as “Not Secure”. This essentially means that the website does not use HTTPS, a form of connection security that uses a certificate to prove the website’s identity to browsers and encrypts information in transit.
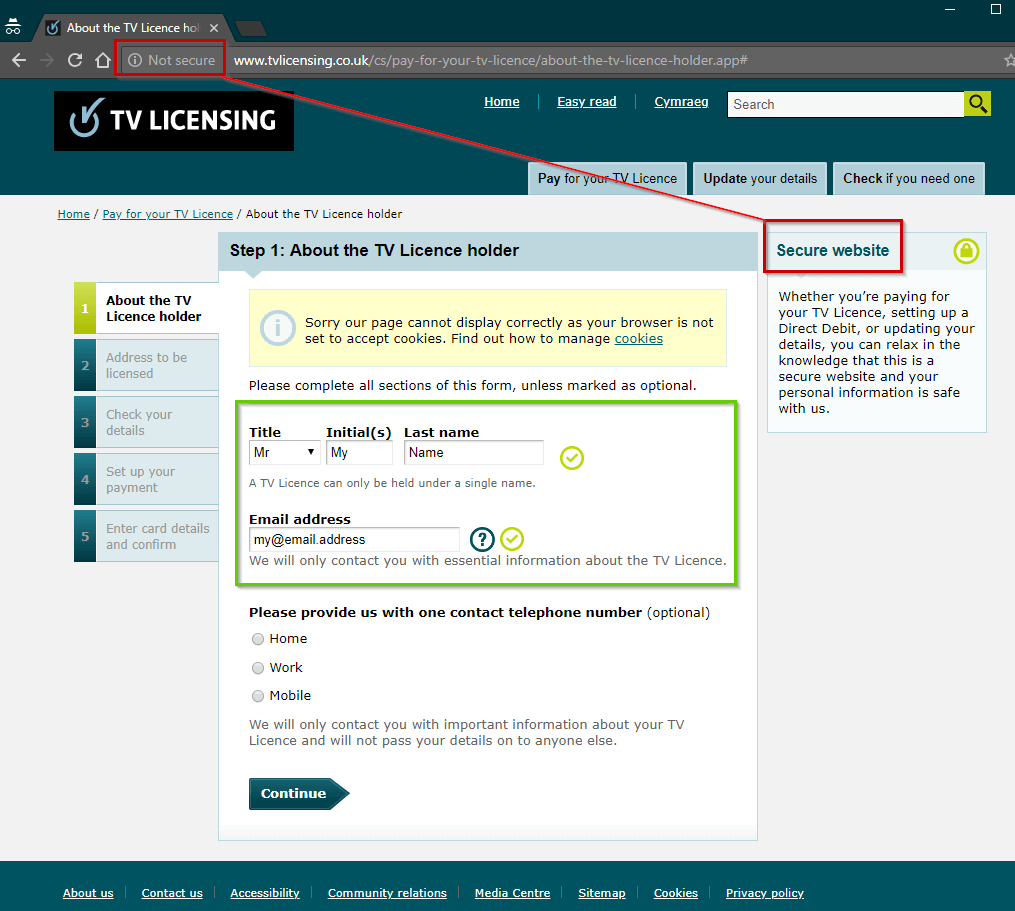
Step 1: Your name and e-mail: Not secure
If we look at Step 1 for applying for a TV license, you can see that despite the website claiming to be a “secure website”, Google Chrome clearly marks the website as “Not secure”. This means the information I am sending to them in green, my name and email address will be sent in plain text and could be intercepted.
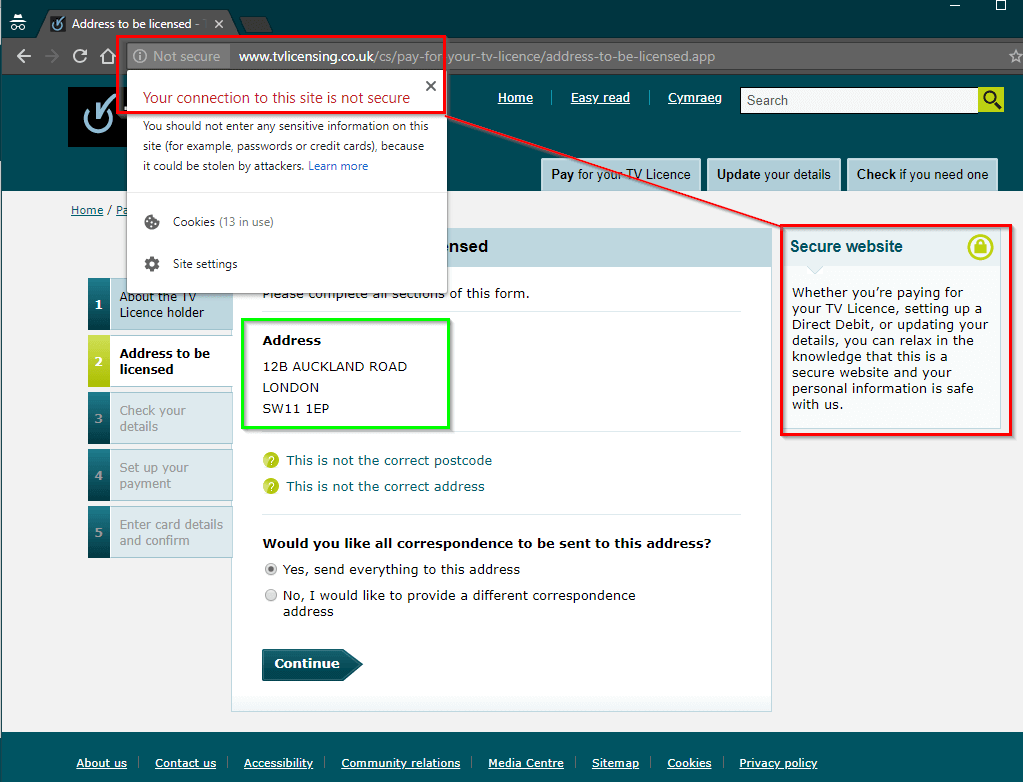
Step 2: Your home address: Not secure
Unfortunately, this trend continues onto step 2. Opening the “Not secure” warning from Chrome specifically tells you not to enter sensitive information into these kinds of websites. Once again, the site claims it is “secure”.
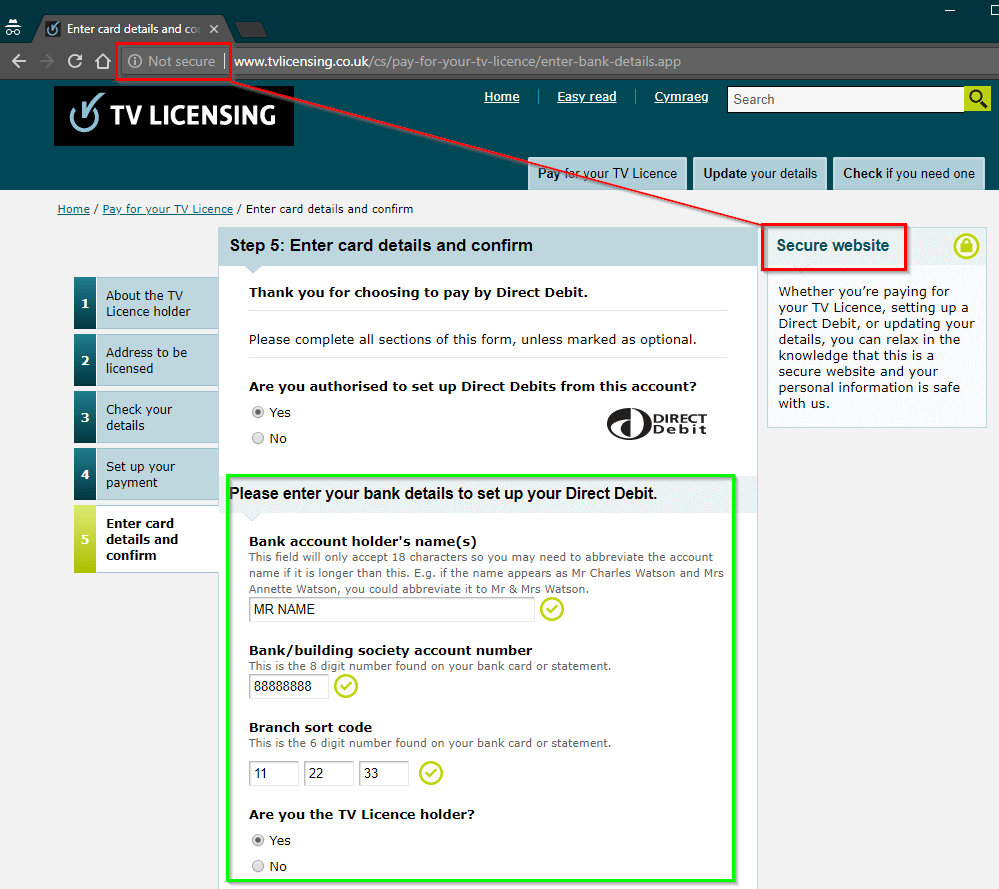
Step 3: Your bank details: Not secure
Well, this is a doozy. I went through the procedure to set up a direct debit and still, even at this stage, I am not being offered a secure connection and yet I am being asked to enter my bank account holder’s name, my account number and sort code. That’s not great.
I let tvlicensing.co.uk know their website is not secure
I sent the @tvlicensing Twitter account a tweet, with screen shots of the unsecure connection process and challenging whether their website really was “secure” as they claimed.
Really @tvlicensing? This is a *secure* website where my personal information is “safe”? cc @troyhunt @BBC#infosec #CyberSecurity #webdev #fail pic.twitter.com/MMjd0ZJ6tU
— 🅼🅰🆁🅺 🅲🅾🅾🅺 != Mark Cook (@thetafferboy) September 3, 2018
Initially, they ignored this tweet. I poked them again several hours later asking them if they could confirm whether or not their website was secure. This is the response I received:
Hi Mark, Our website is secure and our website’s security certificates are up to date, so rest assured, personal details are safe. More info here: https://t.co/dLNMy88xd8
— TV Licensing (@tvlicensing) September 4, 2018
Somewhat ironically, the URL they provided to prove the website is secure, is, you guessed it, also insecure.:

Does it actually matter?
In a word, yes. The most common misconception is that secure HTTPS connections are only required on pages that are highly sensitive, such as processing payments. The UK’s own National Cyber Security Centre advises that “all websites should use HTTPS, “even if they don’t include private content, sign-in pages, or credit card details.”
Without an HTTPS connection, your browser has no way of verifying that the information your receiving is from the website you think it is. This leaves you open for a myriad of potential problems, such as attackers being able to inject extra code into the page you’re looking at, without your knowledge.
Even if only your name and e-mail address was sent over an unencrypted connection, this is enough for a potential attacker to act on. Knowing the name, e-mail address and time that customers were purchasing TV licenses gives you all the information you need for a quick-response phishing e-mail. Imagine signing up for a TV license and within an hour, receiving an official looking e-mail, addressed to you, saying that your payment for the TV license you just bought failed. No problem, just [click here] to pay again, on the attacker’s very convincing looking website.
There are people way smarter than me that do a great job of explaining why even your static website needs HTTPS
Why is TV Licensing not secure?
Well, a little digging shows that they do have a secure version of their website, it’s just that you need to manually type in the ‘s’ after the http, which is of course, ridiculous. If you perform a Google search for the TV Licensing website, Google lists the insecure (HTTP) version:
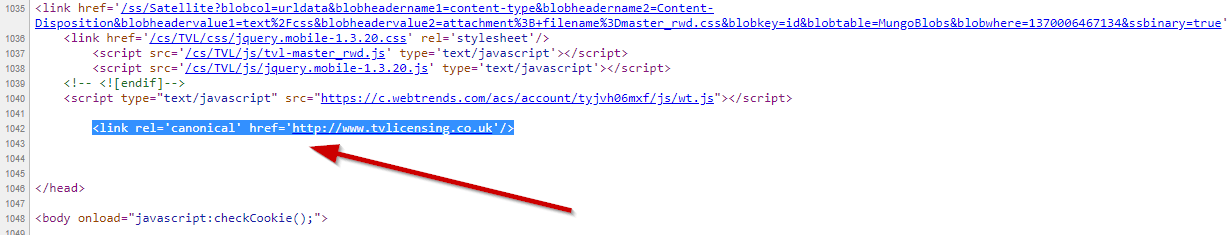
Part of the reason for this is that the TV Licensing website specifically tells search engines to use the insecure version over the secure version by using a canonical tag.
How they can fix it
As many commenters in the thread have pointed out, the easiest fix (in addition to the above) is just add the few lines of code to redirect all http: requests to https:
How many people are affected?
A quick Google search shows there was £3.7Bn collected in license fees in 2016/17.
To get some rough numbers, if we assume everyone paid their £150, that’s around 24.5M TV licenses, right? Even if only 1/4 of these people pay for their licenses online, that’s 6 million license transactions that are affected.
Ask them to get secure
Why not ask @tvlicensing to secure their website? They handle way too much data to treat it with such disregard.
Update (5/9/18): TV licensing website is down
It would appear that the tvlicensing.co.uk website is down for “planned maintenance”.
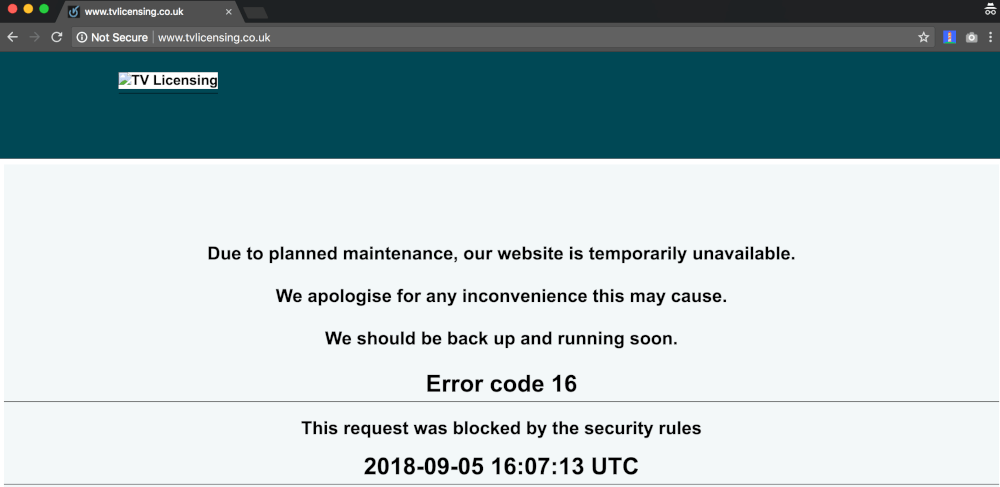
Their Twitter account, however, suggests it may not be planned:
We are having issues with the TV licensing website, and we will restore the website as soon as we can.
— TV Licensing (@tvlicensing) September 5, 2018
Update (6/9/18): Estimates of numbers affected are projected for 1 year
I would like to make clear that this post was written after tvlicensing.co.uk had publicly tweeted there were no security issues with their website. Please note; the calculation of affected users is a yearly estimate on users are being processed, assuming nothing changes – not necessarily users that have been processed.
Update (8/9/18): TV licensing website is back online
The tvlicensing.co.uk is back up and running and they have made the site more secure by switching to HTTPS. They have published a page of FAQs about the security flaw and saying the issue only persisted for 8 days, between 29th August – 5th September, but do not provide figures as to how many customers have been affected. If my estimates below were anywhere near accurate, my guess is that a conservative estimate might be around 130,000 people, at least for personal details.
Some of the damage-control statements they have made are more than a little disingenuous, in my opinion, which makes me think they’ll likely have a similar situation in the future.
“As soon as we discovered this issue we took the website offline and fixed it.” – that’s not true. @thetafferboy had to mobilise many people to make you actually listen when he pointed out there was a problem. You tried to fob him off.
— I, Dom Davis (@idomdavis) September 8, 2018
It did surprise me that they still haven’t given any clear comment, path or remedy to the issue they faced with getting an important, but slightly technical request from the ‘frontline’, to the people that needed to see it.
The important thing is that they’ve at least fixed this main issue. Thank you to all my fellow concerns humans and infosec people that helped make enough noise to move them into action.
For those that don’t know about it, there is a browser extension called HTTPS Everywhere created by the Electronic Frontier Foundation and Tor Project that will automatically push you to the HTTPS version of a website, if it exists.